This article explains how to configure a Vault Connector used by the Cloudiway cloud migration platform.
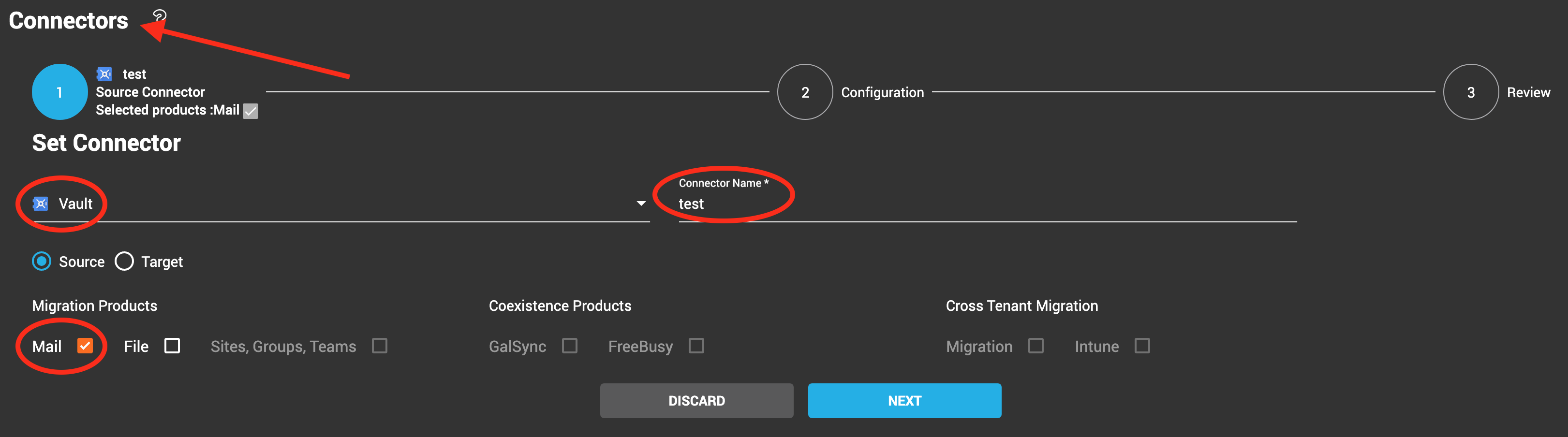
Go to Connectors, click NEW, and select Connector Type Vault.
Enter the Connector Name, and check Mail as the product.
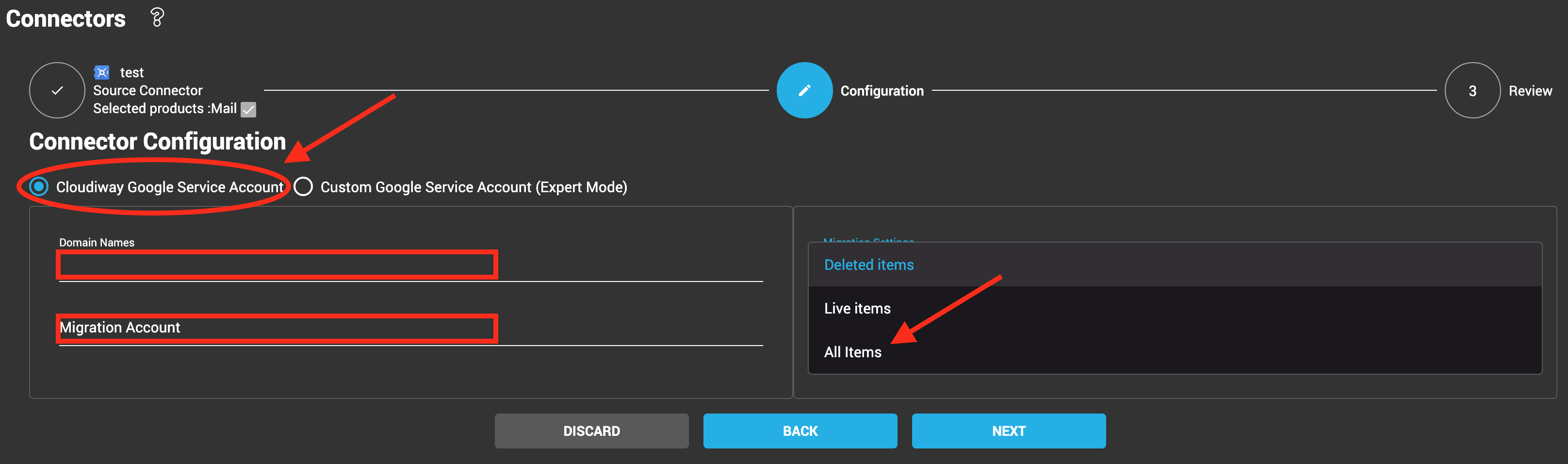
Click Next, and you will see the connector configuration page where you have 2 options:
1. Either use Cloudiway’s Google Service Account:
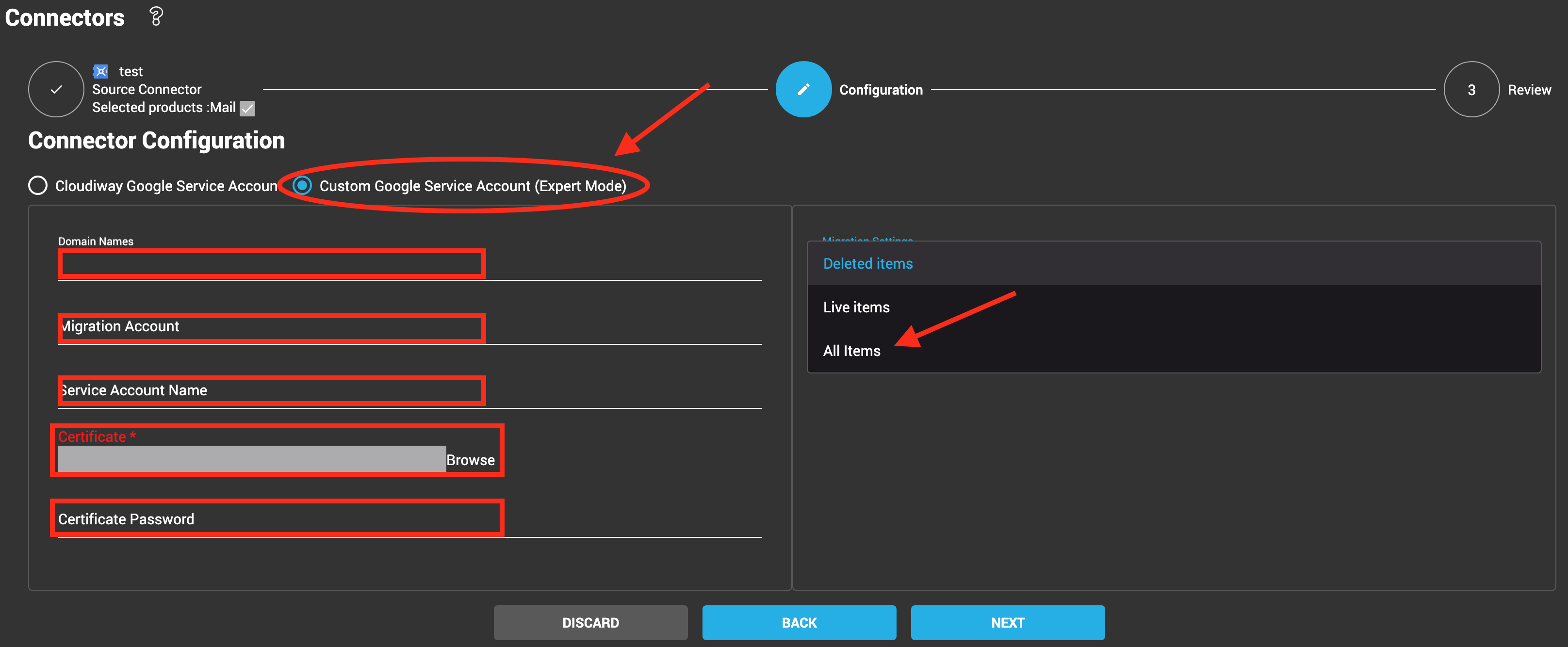
2. Or define and use Custom Google Service Account:
For more details on the creation of a custom google service account, you can click here.
For both options, you have to populate these fields:
- Domain Names: enter the Domain Names to manage.
- Migration Account: most of the Google APIs need an account to impersonate (run on behalf of), enter the email address of that account here.
For best results, the migration account specified should be administrator (super admin) of the tenant for Google Site, Groups, Team Drive migration, or GALSync, and Free/Busy. It is not used for Mailbox and Drive migration. If you do not wish to use a super admin account for this, the migration account specified must have appropriate admin/owner/manager rights manually applied to each of the source items to migrate; every site, Team Drive, etc.
It’s for the migration connectors where we can level down the super admin account to the appropriate admin/owner/manager for each corresponding Google workload to migrate.
For more information, please read: Do I Need A Global Admin Service Account For Cloudiway?
- Migration Account Password: Enter the password of your migration account. Please make sure the password will not change or expire during the project.
- Phone Number and Favorite Login Location are required by Google Site and Google Groups migration (Google may ask to answer security questions if it detects login from an unusual location).
- Google service account which is not the migration account specified above:
- The Cloudiway Google service account is always the same and its Oauth 2 client ID is 114818336788408865729. You don´t need to enter anything in the connector for this option.
- The custom Google service account must be created following these steps and the Oauth 2 client ID will be unique to each customer. Enter the service account name, import the certificate and provide the certificate password.
Click on NEXT then COMPLETE.
More Information:
Product : Email Archives migration
Solution : Migrate Google Vault to Microsoft 365